IT-security consultancy areas and expertise
If you are able to easily understand if your risk, security and compliance level are better, worse or the same as yesterday, how would that affect your business decisions?
Helping you in any area, from start to end or just between

Trusted Advisory & Strategy
Trusted senior advisory, with +20 years broad IT-Security and industry experience in finance, public and managed services sectors, that has the ability to interpret business needs and translate them to relevant security measures. Extremely valuable if you need to exchange ideas and get second opinion, developing strategies or, assessing current state when planning for future.
IT-Security architecture and design
Providing competences within architecture, design and IT-security related projects, for high security or PCI DSS regulated solutions, where we can help you plan, design, role out and review solutions to ensure that they are compliant towards the regulation and requirements that affect you, providing expertise at highest level.

Risk Management
Carolina Reaper Chili, it is harmless in initial development state, but in a few month it will change its characteristics to one of the hottest chilis in the world. Risk management is all about understand and adapt to current state of the situation, and based on frameworks as ISO27005, and long experience I help you to identify, prioritizes and mitigate threats and vulnerabilities that provide you with an business risk. leading and guide you through workshops, visualization and reporting, providing tangible, business aligned, recommendation how to proceed.
Security visualization
Making informed business decisions is often based on gut feeling and the “it worked yesterday” principle, but would be much more credible if it is based on comprehensible data and actual risk.
Helping you to understand your data from a security and compliance point of view, utilizing your current BI solutions. Through use cases that includes importing, analyzing and corelating reports and data from your current tooling you get an a new understanding of your overall security posture.


Cyber Resilience
As an zombie apocalypse. currently seems unlikely, planning for the worst and most unlikely, give you a preparedness and ability to conduct business in disrupted situations. Based on your business needs, assess and test your important business processes, with relevant suppliers and stakeholders. Helps you identify systems maximal tolerable downtime (MTB) and related interruption to business, and based on the outcome, providing recommended measures. In cyber resilience and continuity management, there are a need, for critical systems, to understand the full spectra of security posture, how vulnerable you are to attack, where we assess, analyze and help you in the vulnerability prioritization work.
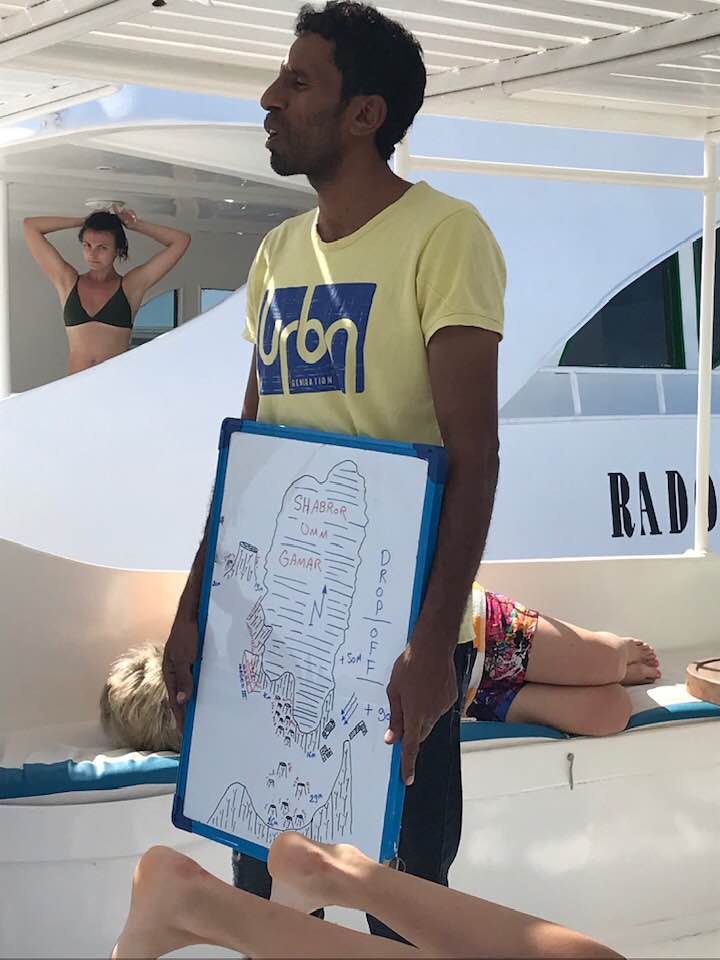
Strategic and advisory
Planning ahead is a key factor for success, as in the picture where a dive guide describes what to anticipate during a dive prepares you for coming future. Same is true for your business, if you have an idea where you go and what you will meet, you will be in a good position. We assess and analyze your current security posture, maturity and capabilities to predict, prevent , detect and respond to unwanted activity. Based on the outcome we provide an strategy and roadmap with defined outcome to strengthen your ability to perform. We provide guidance and hands-on activities to assist you in every step on the way. Providing guidance, plans and insight.

Policys and frameworks projects and audit
Wether in youth sports, or hightech business, policys, rules and frameworks are key to regulate any interactions and business, with knowledge about PCI DSS, ISO27001, CSA and similar frameworks we can help you plan, design, role out and review soultions to ensure that they are compliant towards whatever regulation you need.
